Security Recommendations
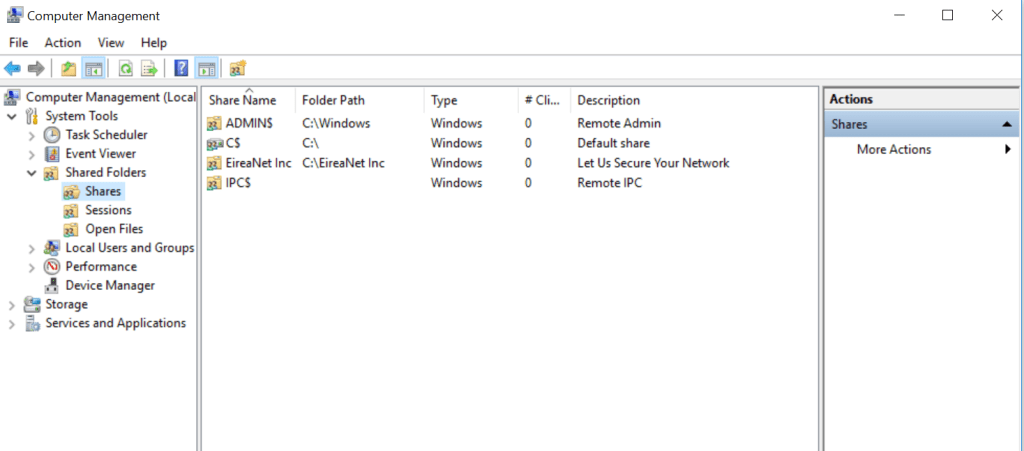
We provide a comprehensive list of vulnerabilities and remediation options on this page for our visitors’ reference. However, we would like to inform you that EireaNet, Inc. offers a free of charge automated mitigation service to our monthly subscribers. This service is designed to detect and remediate any vulnerabilities or other security issues on your system.
Our mitigation service is constantly updated with the latest threats and vulnerabilities, ensuring that our subscribers are always protected against the latest security threats.

Protect your business with our free mitigation services:
In addition to the automated mitigation service, EireaNet, Inc. also provides personalized consulting for businesses that require a more tailored approach to their security needs. Our team of experts can conduct thorough security assessments and provide customized recommendations to address specific vulnerabilities within your system.
Covered Categories.
-

Security controls (Firewall)
This setting disables merging of local Microsoft Defender Firewall connection rules with group policy firewall rules for the Public profile. It prevents local administrators from creating connection security rules that could weaken the Group Policy settings and expose the system to remote attacks on a public network. Read more
Last Modified:
-

Application (Microsoft Office)
The Office automatic updates can be enabled or disabled through Group Policy or registry settings to ensure timely application of security updates. Enabling automatic updates helps prevent malicious attacks and ensures device security. Additionally, hiding the UI options to enable or disable updates prevents users from interfering with these settings. Options for remediation include Group… Read more
Last Modified:
-

Application (Google Chrome)
Google Chrome offers various settings to enhance security and privacy. Disabling background apps when the browser is closed prevents vulnerable or malicious processes from running. Additionally, disabling the password manager feature prompts users to manually enter their passwords, reducing the risk of unauthorized access. Enabling the block third-party cookies feature enhances privacy by preventing website… Read more
Last Modified:
-

Security controls (Exploit Guard)
Controlled folder access can be set to enabled or audit mode in Windows Defender Antivirus to protect key system folders from malicious apps. Failure to enable it exposes systems to attack. Remediation options include setting Group Policy or registry values to enable controlled folder access. Audit mode allows monitoring without blocking apps, while enabling the… Read more
Last Modified:
-

Application (Adobe Acrobat)
This page provides guidance on disabling Flash and JavaScript in Adobe Acrobat Pro XI and Adobe DC. Flash is highlighted as unsecure with known vulnerabilities, advising against its use. Disabling JavaScript is recommended due to its potential for misuse by attackers to manipulate users or execute undesired code. The referenced sources from CISA provide further… Read more
Last Modified: